Beware of Phishing Scams at CSULB
Did you know research shows that the research/education sector is the most targeted by cyberattacks? Yup. So recognizing and reporting phishing emails is a shared responsibility at CSULB.

Spot It
Learn from some of the most common and successful phishing emails that have recently targeted CSULB employees and students:
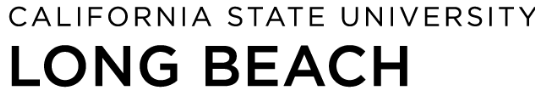
Job Opportunities - These emails quite often come from compromised CSULB accounts and lure recipients with unsolicited job opportunities that often sound too good to be true. They provide basic job information and easy qualifications and direct you to email someone at a non-CSULB email address for more details. These scams have been known to lure you into providing personal and sometimes financial information and leading to loss of money.
Image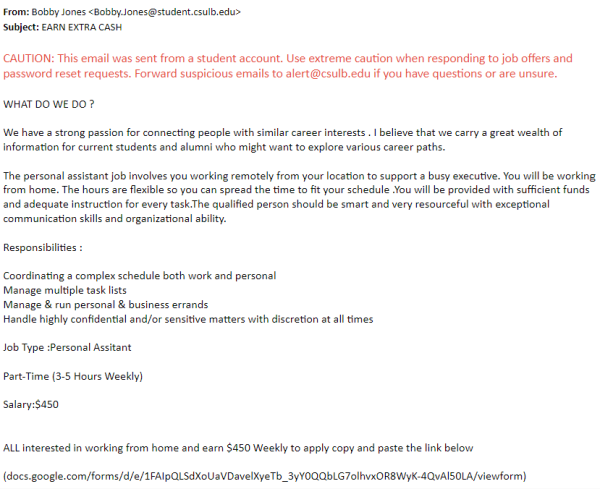
Password/Email Verification - These types of emails ask you to verify, confirm, update, keep your account credentials and provide a link to a fake webpage, often imitating a Microsoft or Google page. These emails are attempting to collect your username and password, giving a hacker instant access to your account for further use and malicious intent.
Image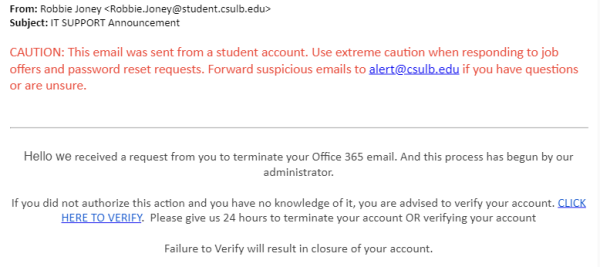
Documents Shared with You - Hackers will try to impersonate people at CSULB, such as someone in the HR department, the Technology Help Desk, or even a colleague, or another CSULB student. These types of phishing emails might ask you to click on a link to access a document with enticing but fake subject matter. These emails are usually attempting to steal your username and password.
Image
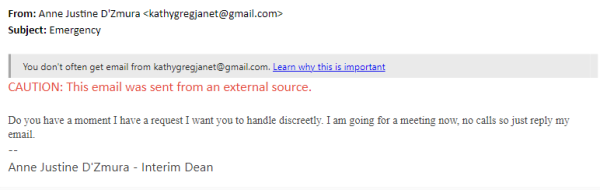
- Quick Tasks - These scams often appear to come from a management-level colleague but from a non-CSULB email account, like Gmail, and asking if you’re available for a quick favor. These often develop into attempts to get you to make purchases of gift cards.
Want to Learn from More Real Examples?
- Visit our Phishing Tutorial for real examples and tips (login required).
- See recent, real phishing examples with tips for avoiding these scams by visiting our article Don’t Get Phished – Identify Malicious Emails and How to Protect Yourself.
- View the ongoing list of phishing emails reported to Division of IT on our Phish Bowl site.
Report It
- If you use the Outlook online app for your CSULB email, you can report phishing emails to Microsoft to improve our email filtering.
- If you think you may have encountered a phishing email, you can forward it to alert@csulb.edu. We can help you determine if it’s a phishing email. Whatever you do, do not click on any links, reply to the email, or send it to anyone else!
Get the Best Protection for Your CSULB Account
Know about our Multi-Factor Authentication (MFA) Top Tips
As a student or employee, you're required to use MFA at CSULB. Ensure you're making the best of it with our tips for the best security.
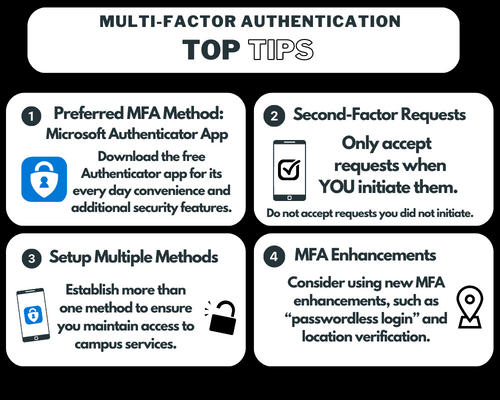
- Use Microsoft Authenticator app for its every day convenience and additional security features. If you're using SMS text or phone calls for MFA, you are more vulnerable to scams.
- Only accept second-factor requests when you initiate them.
- Set up multiple multi-factor methods to ensure you maintain a backup and can always access campus services. Learn how to manage and change your default MFA login methods.
- Use "passwordless login" for logging into your campus account.
More Fun and Learning Opportunities
Want to test your phishing knowledge?
Check out Google’s Phishing Quiz.
How to Avoid Job Scams + Spot Fake Job Offer Letter
CSULB is not affiliated with the creator of this video.